Money is often called the source of all evil, and it's no wonder the internet is rife with corruption and scams. Criminals—often tech-savvy individuals—invent ways to rob people of everything they've worked hard for. The way we use internet-based applications these days makes us highly vulnerable to online scams. We need to be alert, cautious, and smart with our browsing habits, as malicious internet organizations are constantly evolving how they deliver scam content. Luckily, there are some common signs that can help you identify scams. However, until you train your eye to spot intent, you may fall victim. Below you'll find a few common internet scams that can help you browse more safely. This list is by no means complete, so treat everything you do online with caution and vigilance.
Letter Scam
Internet criminals don’t always originate from first-world countries. Many scams come from poorer countries where the exchange rate makes scamming profitable. A common scam involves a letter from a government official or royalty, often from countries such as Nigeria. These criminals write heartfelt letters requesting help to recover money from offshore accounts. The victim is asked to deposit money into the scammer’s account to release millions of dollars, of which the victim supposedly receives a percentage. This is simply false. Once the criminals have your money, communication stops and you're left wondering what happened.
Warning signs include offers that seem too good to be true, unknown senders, or emails full of spelling and grammatical errors due to poor English.
How to avoid: Never reply to emails like this. Avoid clicking any attachments or links. The best action is to delete the email or report it to authorities if appropriate.
Phishing Scams
This is the most common scamming method. Emails appear to be from large corporations or individuals, looking like legitimate communications—such as bill payments or security alerts from your bank. They use eye-catching offers or scare tactics to get you to click a link. The link takes you to a fake website asking for personal login credentials like email or PayPal passwords. Once given, scammers steal your information and may transfer money from your accounts, which is often unrecoverable.
How to avoid: Never reply or click links in suspicious emails. Legitimate organizations will never ask for personal information via email—they already have it. If in doubt, contact the company directly by phone or visit their official website by typing the address yourself, then verify the email's authenticity.
Ransom or Threat Attacks

Fear makes people vulnerable. Often, users download or click attachments only to find their computer infected with ransomware, which encrypts files and demands payment for decryption. Other threats may include emails threatening harm to loved ones or making false accusations.
Signs to watch for include poor grammar or messages with baseless claims. Any email demanding money in exchange for something threatening should be questioned.
How to avoid: Never open unexpected email attachments. Only open attachments when you are 100% sure of their content or if you are expecting them. Never give your information to strangers. Once your data is out, it’s only a matter of time before criminals use it against you.
Facebook Scam

Facebook connects us with friends and family and stores personal information, but criminals love social media for the same reasons. Malicious users can harvest your sensitive data through enticing pictures or games. Innocent clicks can trap you in data-harvesting schemes.
Fake apps or posts often have clickbait or shocking titles such as “Wait till you see what happened to this girl after she swam in the ocean” or “See this celebrity’s naked pictures.” If a second page requires extra steps to view the content, that’s a red flag.
How to avoid: Avoid shocking or disturbing content on Facebook. Use Google to research suspicious titles before clicking. Check your app permissions regularly and only allow access to apps you trust 100%.
Fake Anti-Virus Warnings
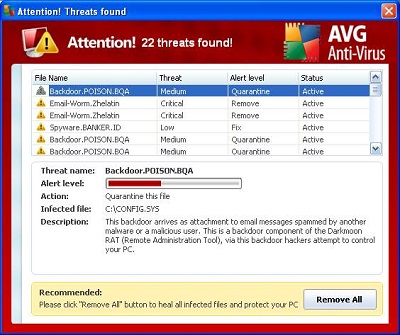
This scam is common on illegal download or adult websites. Users are redirected to fake antivirus alerts mimicking AVG, McAfee, or Windows Blue Screen of Death. The message prompts you to call fake Microsoft support or renew fake antivirus subscriptions. If you follow instructions, scammers remotely access your computer, showing normal Windows error logs as proof of infection.
Warning signs include threatening language like “Your computer is at serious risk” or popups over the website you intended to browse.
How to avoid: Close popups using the keyboard shortcut Alt + F4 instead of mouse clicks. Ignore warnings from antivirus software you don’t have installed. Enable popup blockers and keep your browser updated to reduce risk.
